For most tasks, the official Platform Tools are sufficient and much safer than third-party automators.
The ADB Enable Automator represents the classic tension between functionality and security. While it provides undeniable value for legitimate high-volume technical work, its reliance on unofficial distribution channels and its potential for misuse cannot be ignored. Users and organizations must weigh the time saved against the risk of compromise, ensuring that such powerful tools are only sourced from trusted environments and used within a clear ethical framework. As mobile operating systems become more locked down, the drive to automate will only increase, making the scrutiny of these tools more vital than ever. Quick Tips for Safe Handling
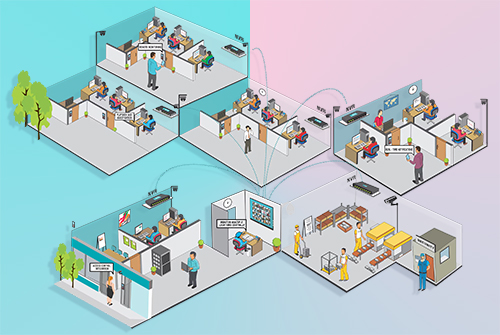
For developers managing "device farms" or IT administrators configuring hundreds of enterprise-locked handsets, manual intervention is a bottleneck. An ADB Enable Automator aims to streamline this by using pre-defined scripts—often packaged in compressed formats like RAR for portability—to navigate system settings or exploit specific bootloader states. By reducing the time required to establish a shell connection, these tools allow for rapid software deployment, automated testing, and efficient troubleshooting. In this context, automation is not merely a convenience; it is a prerequisite for industrial-scale mobile operations.
In the rapidly evolving landscape of mobile development and device management, the Android Debug Bridge (ADB) serves as the primary gateway between a workstation and an Android device. While enabling ADB is a straightforward manual task for a single user, the need for "ADB Enable Automator" scripts has grown within large-scale development environments and device refurbishment centers. However, the convenience of automating a core security toggle brings forth a complex debate regarding technical efficiency versus the erosion of device security protocols.